Stepping Into the Future: Industry Tips and Trends for Podiatry Practices
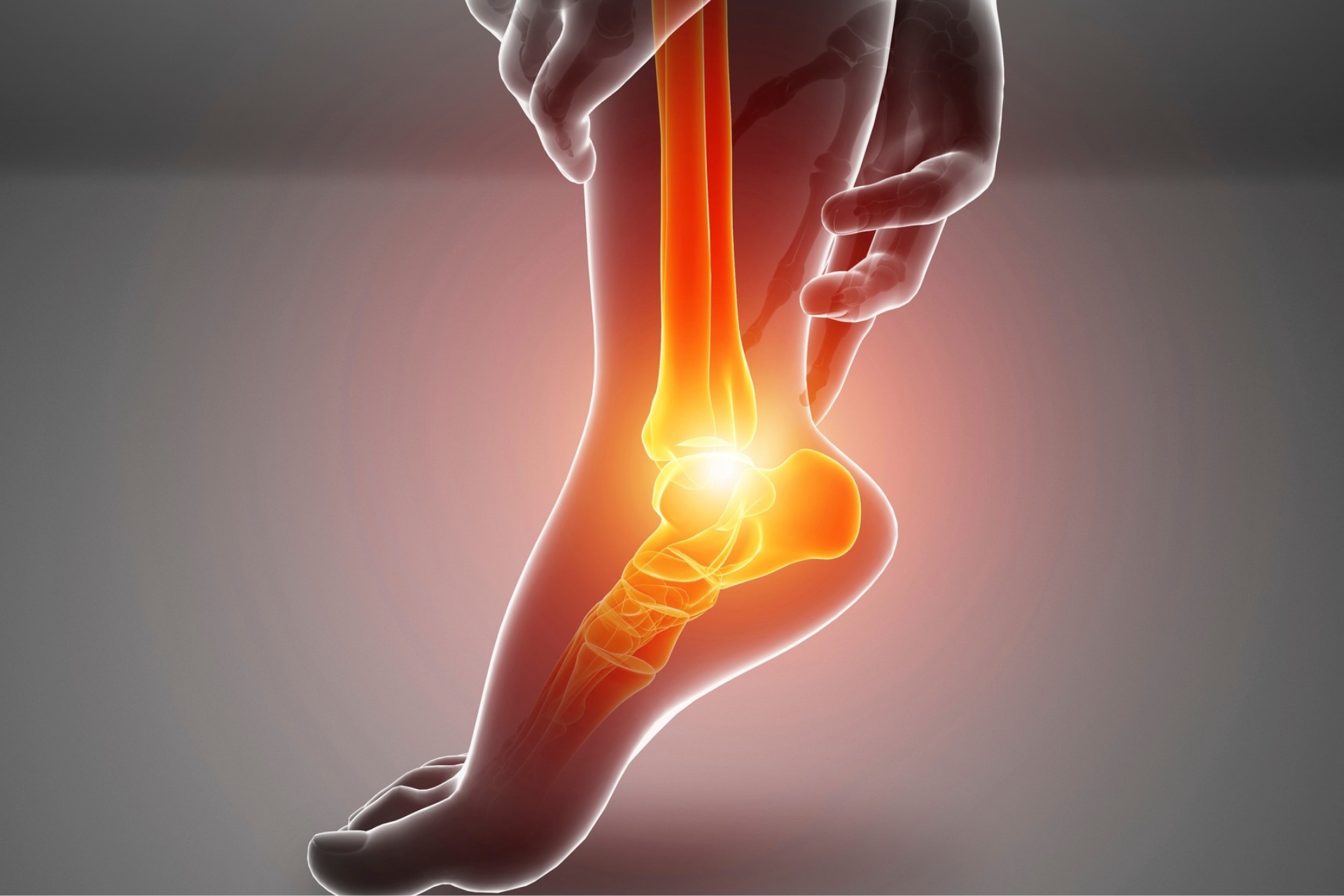
Stepping Into the Future: Industry Tips and Trends for Podiatry Practices Podiatry practices play a vital role in maintaining the health and mobility of individuals, addressing issues from common foot pain to complex surgeries. As the medical field evolves, podiatrists must adopt innovative techniques and technologies to meet growing patient needs. One exceptional Podiatrist in Statesboro GA leading the way in modern podiatric care is Affinity Foot and Ankle Specialists. Their commitment to excellence and innovation serves as a benchmark for the industry. Adopting Advanced Technology Technology is transforming every facet of healthcare, and podiatry is no exception. Advanced imaging tools such as 3D foot scanning allow podiatrists to diagnose and treat conditions with unparalleled accuracy. These tools provide detailed insights into foot structure and abnormalities, ensuring personalized treatment plans. Practices like Affinity Foot and Ankle Specialists leverage these technologies to stay ahead in providing precise and effective care. The Rise of Minimally Invasive Procedures Minimally invasive techniques are revolutionizing podiatry, offering patients quicker recovery times and less postoperative discomfort. From bunion correction to plantar fasciitis treatment, these procedures …